Build WordPress Sites That Stay Under Your Control
For small business owners who want to replace SaaS stack with a unified, owned infrastructure. Learn the architecture-first method that keeps your costs fixed and your data under your control.
William walks through why most small business owners overpay for fragmented software, what it costs them beyond dollars, and the architectural shift that changes everything.

See the four failures in fragmented systems and how unified architecture solves them (5:13)
Download the Architectural Risk Assessment PDF HereWhy Fragmented Doesn’t Work
Most small business owners run their operations on multiple platforms. A course platform here. An email system there. A community tool somewhere else. It seems fine at first, because each tool works. But they were never designed to talk to each other.
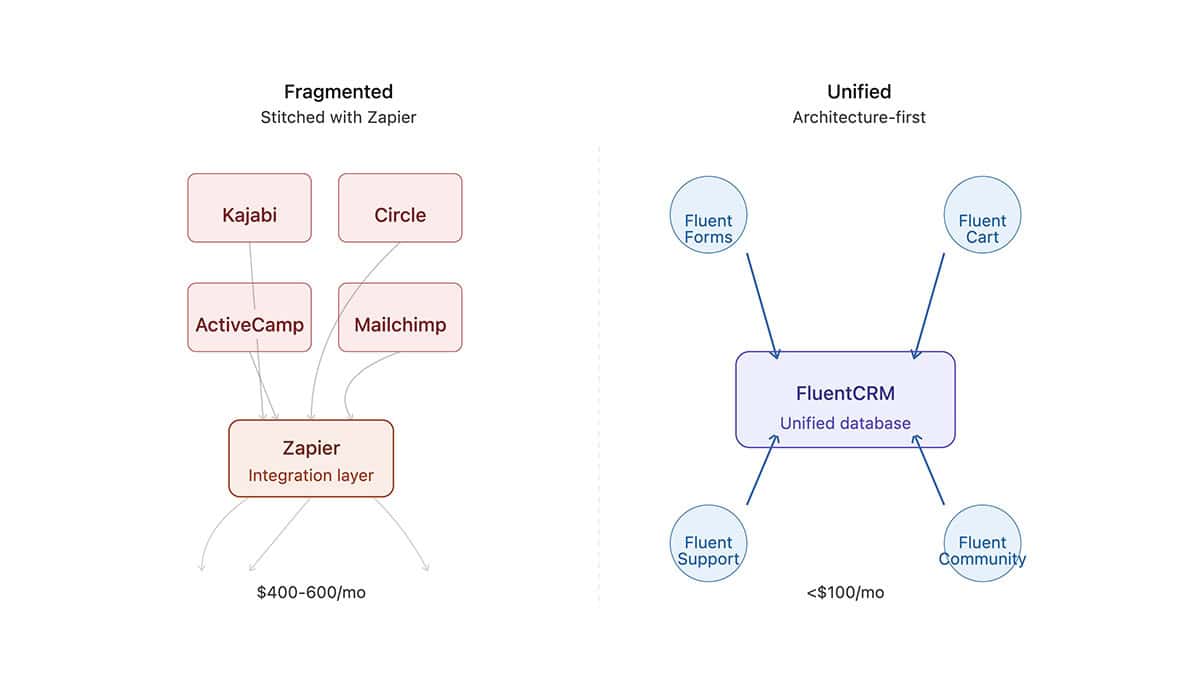
So you use Zapier to connect them. Your bill goes up. Your integrations break silently. And every time your business grows, your software costs grow with it. Not because you’re getting better features, but because platforms charge by contact count, member count, and task count. You pay for success, not capability.
The deeper issue isn’t the tools themselves. It’s the architecture. You built your business on a foundation that was never designed to hold what you’re building on top of it. And that creates five specific structural failures that compound over time.
The Three Architectural Principles
Every aspect of our method is built on these foundations.
Interoperability
Tools designed to work together eliminate integration friction. Fragmented systems require constant translation between incompatible databases and automation languages. A unified architecture means your tools natively speak the same language. No Zapier, no API failures, no silent breaks.
Performance
Unified infrastructure is faster. No relay services, no translation layers, no task queuing. Data flows directly from collection to action. Your customers experience snappier checkouts and faster access. Your automations execute immediately, not after a third-party service processes them.
Security
You control your data, your servers, and your compliance obligations. No third-party platforms holding your customer data. No unknown jurisdictions are processing transactions. We teach hardening with Cloudflare security rules, controlling access, and maintaining complete audit trails of every customer interaction.”
The Architecture-First Approach
Instead of stitching tools together after purchase, start with architecture. Ask: “What do I need my business infrastructure to do?” Then choose tools that were designed from the ground up to do it together.
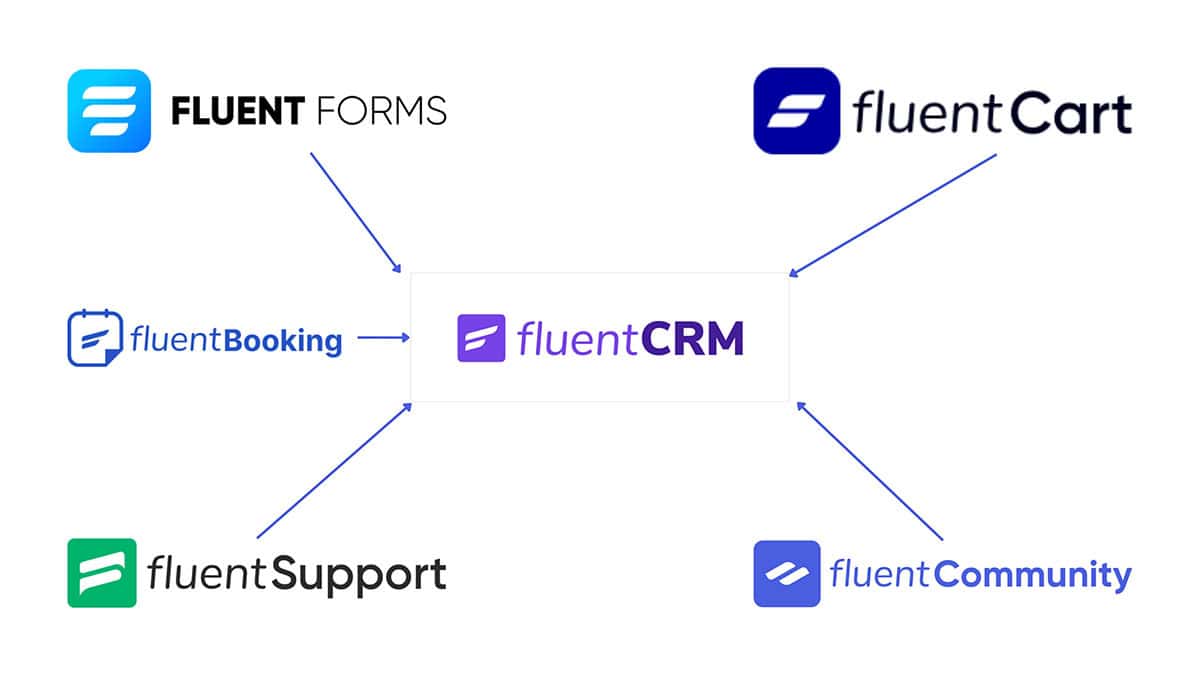
This is what the Fluent ecosystem does. FluentCRM is your unified customer database. Email, CRM, automation logic. It all lives in one place. Every other tool feeds customer data into FluentCRM. Your forms, checkout, course platform, community, booking, and support. You have one complete view of every customer interaction.
Your automations run from one place. Your costs stay fixed as you grow. Your data belongs to you, not a vendor. And your business roadmap is controlled by you, not by a platform’s development priorities.
This isn’t a philosophy. It’s a structural shift that changes how your business infrastructure scales, performs, and stays secure.
Ready to Own Your Infrastructure?
Start with a clear-eyed assessment of where you are and what needs to change.
Download the Architectural Risk Assessment PDF. Get a detailed analysis of the five structural failures hiding in your current setup.

