Why the EssentialPlugin WordPress Plugin Backdoor Feels Like the 2011 RSA/Lockheed Attack
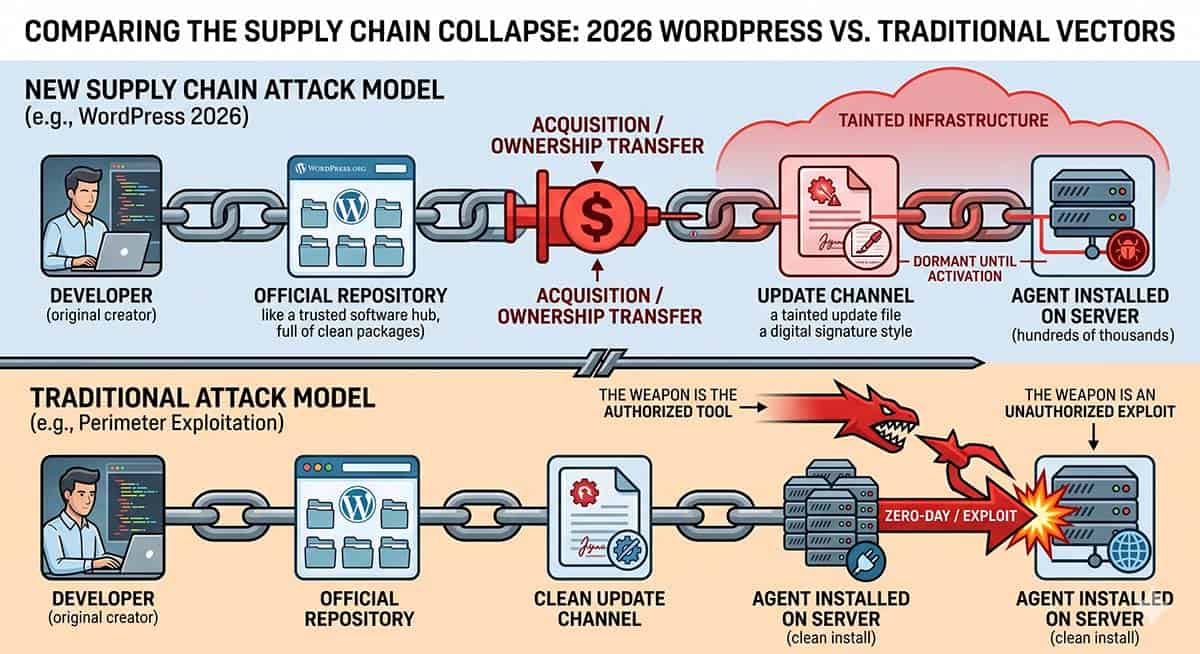
The Essential Plugin breach (CVE-2026-6443 on April 7, 2026) is a WordPress plugin backdoor attack, not a WordPress platform vulnerability. An anonymous buyer purchased the plugin suite on Flippa.com, planted backdoors in the update channel, and activated them across 400,000 sites. This follows the identical pattern as the 2020 SolarWinds breach and the 2011 RSA SecurID crisis. The defense does not live in auditing your software. It lives in restricting your network traffic. SaaS tenants cannot implement this defense at all, which makes the SaaS Hostage Crisis a structural security problem, not a vendor inconvenience.
The Public Debate Is Asking the Wrong Question
The conversation around the Essential Plugin compromise has already drifted in the wrong direction. Commentators are framing this as a WordPress platform vulnerability, and in doing so, they mistake the vehicle for the weapon. This incident belongs in the same case file as the 2020 SolarWinds breach and the 2011 RSA SecurID crisis, because all three follow the same architectural logic: the platform held. The trust in the agent failed.
What a WordPress Plugin Backdoor Actually Is
Most security threats enter through the front door. A phishing email tricks an employee. A misconfigured server exposes an open port. A weak password fails under brute force. Your security team trains for these scenarios because they follow a recognizable pattern of intrusion.
A WordPress plugin backdoor enters through a door you built yourself and left permanently open.
Rather than attacking your infrastructure directly, an adversary compromises the software you already trust and run on your systems. They do not need to find a flaw in your defenses. They need to find a flaw in the chain of custody between the plugin developer and your server. Once they corrupt that chain, every site running the affected plugin becomes compromised at the moment of the next routine update. Your own maintenance process becomes the delivery mechanism.
The attack succeeds precisely because it exploits trust rather than circumventing it. You authorized the plugin. You configured the update channel. You accepted the patch. At every step, you acted in accordance with your own security policy. The corruption happened upstream, outside your visibility and beyond your control.
The WordPress Plugin Backdoor Pattern Your Security Vendor Will Not Mention
I was a Lockheed Martin employee in 2011 when adversaries stole the RSA SecurID seed values. The moment those seeds were compromised, every authentication token in our infrastructure became a liability rather than a control. That breach gave attackers legitimate credentials to walk through the front door rather than a vulnerability to exploit. Thousands of employees, myself included, lost remote access and had to report to physical facilities because the trusted agent had changed allegiance.
Years later, at Lucent, I watched the SolarWinds Orion agent execute the same transformation, turning authorized network monitoring software into the delivery mechanism for Russian intelligence. The organizations it compromised were not negligent. They were running patched, licensed, monitored software from a reputable vendor. The pattern repeats because the architectural flaw is permanent, not incidental.
Someone purchased Essential Plugin through a commercial acquisition, planted dormant backdoors across the suite, and activated them earlier this month to distribute malicious code to every site running the affected plugins. The attacker needed no zero-day exploit. They bought the keys to roughly 400,000 active installations and used the legitimate update channel that those site owners trusted to deliver their payload. The site owner’s authorization became the attack vector.
In this attack, the malware appended itself to the very end of the wp-config.php file and used it to inject a massive block of PHP code. Simply deleting the plugin was insufficient to correct the damage.
Warning for Site Owners: Deleting the affected plugins is insufficient. The exploit injects 6KB of malicious code directly into wp-config.php. Verify your file size and inspect for the wpos-analytics payload immediately.
How a Supply Chain Attack Works Once It Activates
When a backdoored plugin activates, it does not announce itself. It establishes a silent outbound connection from your server to a command-and-control address that the attacker controls. Your firewall logs show normal traffic. Your monitoring tools report clean operations. The agent begins exfiltrating credentials, harvesting session data, and waiting for further instructions, all while your standard security stack reports a healthy environment.
The reason your tools miss it is architectural. Most security monitoring focuses on inbound threats: unauthorized access attempts, known malicious IP addresses attempting to connect to your server. The WordPress plugin backdoor reverses the direction. Your own server initiates the outbound connection to the attacker. Many perimeter controls are not configured to interrogate that traffic because the assumption is that outbound requests originate from legitimate software performing legitimate functions. That assumption is the vulnerability.
A WordPress plugin backdoor does not break into your server. It turns your server into a willing participant. Your firewall never fires because your own system made the call.
Why SaaS Tenants Cannot Defend Against a WordPress Plugin Backdoor
A WordPress operator who owns and manages their own hosting infrastructure retains the ability to implement the network controls described below. A business running on a SaaS platform does not.
When you operate as a SaaS tenant, the platform vendor controls every packet that enters and leaves the environment. You receive no visibility into network layer traffic and no ability to configure egress rules. If a WordPress plugin backdoor establishes an outbound connection inside that environment, you have no instrument to detect it and no lever to block it. You depend entirely on the vendor to identify the breach, disclose it, and remediate it on a timeline the vendor controls, with a level of transparency the vendor chooses.
This is not a feature gap. It is the structural ceiling of the SaaS Hostage Crisis: a condition in which the business owner surrenders permanent control of their security posture to a third party whose financial interests do not always align with their protection. The Essential Plugin breach does not create this condition. It exposes it.
If you cannot see the network layer, you cannot defend it. SaaS tenants do not lose this capability through negligence. They sign it away in the terms of service.
The Network Layer Defense That Stops a WordPress Plugin Backdoor
You cannot audit your way out of a WordPress plugin backdoor by reading changelogs or vetting developer reputations. The defense that works operates one layer below the application entirely.
A backdoor is architecturally inert if it cannot reach its command-and-control server. Strict egress filtering enforces this condition. You define precisely which external destinations your server is permitted to contact and block all other outbound traffic. When the backdoored plugin activates and attempts to call home, it reaches a rule rather than a route. It cannot receive instructions. It cannot upload stolen data. The breach exists in your codebase but has no impact on your infrastructure.
Cloudflare’s ruleset provides the inspection surface to implement this at scale. You configure rules targeting specific plugin directories, flag outbound requests to unrecognized IP ranges, and surface the WordPress plugin backdoor when the agent first reaches an unknown destination. Because the C2 instructions reside on a public blockchain, traditional domain takedowns are ineffective. The backdoor simply queries the next ‘block’ to find its new home.
Detection moves from weeks after data loss to seconds after activation.
Deploying Internal Tripwires and Automated File Integrity
You must supplement network visibility with high-sensitivity file integrity monitoring. Professional security tools like Wordfence or Patchstack can be configured to alert you the moment a core file like wp-config.php deviates from its known-good state. Many enterprise-grade hosting providers now include this at the server level, automatically flagging unauthorized modifications to the site’s configuration before the malicious code can execute its first phone-home.
These tools act as your internal tripwires. They provide the final verification that your digital property remains under your exclusive control, even when the software supply chain attempts to betray that trust.
Why This Defense Works When Application-Layer Auditing Fails
This approach works because it relies on the physics of networking rather than the reputation of software vendors. Ownership changes hands. Developer intentions shift. Vendor reputations dissolve when a commercial transaction closes.
The laws governing packet routing do not change. A WordPress plugin backdoor still requires a channel, and when you control the channel, you control the outcome.
The Distinction That Determines Your Exposure to a WordPress Plugin Backdoor
Every business owner running plugins on a WordPress server makes a daily choice between two security postures, often without recognizing the choice exists.
The first posture trusts the names on the software. It audits code, monitors vendor reputations, reads changelog notes, and assumes that authorized plugins behave as intended. This posture fails the moment a commercial acquisition changes the owner of that plugin without changing its name or its position on your approved vendor list.
The second posture trusts the network’s behavior. It monitors and restricts every packet regardless of which plugin generated it, and it treats outbound connections to unknown destinations as a breach condition rather than routine traffic. This posture was held during SolarWinds for the organizations that had implemented it. It will hold during the next WordPress plugin backdoor incident for the same reason.
Stop auditing the code and start auditing the traffic. That shift is what separates a digital tenant from a sovereign architect, and in the current threat environment, it is the only distinction that reliably matters.
Summary of the 2026 WordPress Plugin Backdoor Crisis
From the stolen seeds of RSA in 2011 to the poisoned updates of SolarWinds in 2020, and finally to the adversarial acquisition of the EssentialPlugin WordPress plugin backdoor in 2026, the vector has shifted from technical theft to commercial takeover.
If this post raises questions about your current infrastructure posture or your exposure to the SaaS Hostage Crisis, the comments section is open. WordPress plugin backdoor prevention requires a structural conversation, not a vendor one.